3 Best Practices to Keep Critical Infrastructure Secure from Cyberthreats
Critical infrastructure has become a prime target for increasingly sophisticated cyberthreats. Operators now acknowledge that future attacks are not a matter of [object Object], but [object Object]. According to the [object Object], the average cost of a breach in the energy sector has climbed to [object Object], with credential-based attacks remaining a top vector.
A global survey by Siemens and the Ponemon Institute found that [object Object] reported at least one shutdown or data loss incident per year. Electric utilities have been especially vulnerable, with up to [object Object] impacted by events like the [object Object]. Recent high-profile attacks on facilities like the [object Object] and the [object Object] have underscored the urgency of strong cyber defenses.
At the center of many of these breaches? [object Object] Weak, reused, or stolen credentials continue to be the common denominator.
To protect critical infrastructure, utilities and energy providers must move beyond the 60-year-old password paradigm and adopt modern authentication practices. Here are three best practices that can dramatically reduce risk:
1. Eliminate Centrally Stored Credentials
Passwords—especially when centrally stored—are a liability. With over [object Object] circulating on the dark web and [object Object] reusing passwords, attackers are finding success with brute-force, credential stuffing, and phishing attacks.
While many organizations deploy MFA as a compensating control, it’s not enough. MFA adds friction, incurs costs, and can be bypassed using phishing kits and social engineering.
[object Object] Centrally stored password vaults remain a target. If breached, attackers can gain footholds into networks, escalate privileges, and compromise mission-critical systems.
2. Adopt Immutable Authentication
The [object Object] confirms that stolen credentials remain the most common entry point in energy-sector breaches. The solution is [object Object]—an approach that removes passwords and shared secrets entirely from the authentication flow.
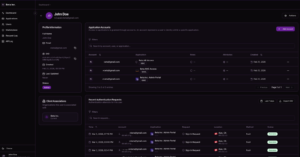
BlokSec Verifiable Identity™ uses decentralized user identities, cryptographic signatures, and tamper-proof ledgers to validate user identity. This:
- Removes password-based vulnerabilities
- Delivers stronger, verifiable user authentication
- Exceeds the protection level of MFA
As CTO Mike Gillan of BlokSec puts it: “Decentralized authentication and Zero Trust go hand-in-hand in securing critical infrastructure. Immutable identity is the future.”
3. Adopt a Zero Trust Mindset
Zero Trust assumes that threats can originate from both inside and outside the network. With thousands of users—from employees to third-party contractors—accessing systems from various locations and devices, traditional perimeter-based defenses fall short.
The core principle of Zero Trust is: [object Object]
This requires:
- Verifying every access request in real-time
- Eliminating implicit trust between systems
- Using context-aware identity verification
Password-based logins contradict this model. Decentralized, passwordless authentication strengthens Zero Trust by ensuring each user’s identity is cryptographically verified at each point of interaction.
Embrace Immutable Authentication with BlokSec Verifiable Identity™
New directives from regulators like NERC and TSA now mandate stronger identity verification at entry points to critical infrastructure. The average breach cost in the energy sector has climbed to [object Object], according to IBM.
BlokSec Verifiable Identity™ enables organizations to:
- Eliminate passwords and reduce credential-based risks
- Align with Zero Trust principles
- Comply with NERC CIP and TSA directives
- Reduce helpdesk load and operational costs