Why are passwords no longer a secure method of authentication?
Passwords have become one of the weakest links in cybersecurity. Despite being in use for over 60 years, they are easily stolen, reused, and cracked—making them the primary cause of data breaches. Businesses and consumers need a modern, password-free approach that ensures both security and ease of use.
TL;DR
Passwords were never designed for the scale or complexity of today’s digital world. Credential-based attacks now dominate breach reports, and hackers can crack weak passwords in seconds. The solution is a shift to unphishable passwordless —secure, fast, and built for the mobile-first era.
A Brief History of Passwords
Passwords were first introduced in [object Object] by computer scientist [object Object] to protect access to personal files in a time-sharing mainframe system (CTSS). His innovation helped pioneer the concept of user-level privacy in computing—but it wasn’t designed for global, internet-scale use.
Fast forward to today: we still rely on passwords to secure everything from email to banking and enterprise infrastructure.
The Cracks Are Showing
According to the [object Object], [object Object] remain the leading cause of reported data breaches. The tools available to attackers have advanced dramatically:
- 🚀 Password cracking tools can test millions of combinations per second
- 🧠 Phishing and social engineering campaigns now leverage AI to craft targeted lures
- 📉 Most users reuse passwords across multiple accounts, compounding risk
The result? Even companies that invest in security infrastructure often expose sensitive customer data when their password defenses fail.
Why Passwords Can’t Keep Up
Passwords have three fundamental flaws:
- They don’t verify identity – anyone with the right string of characters gets in
- They don’t scale securely – managing dozens of logins leads to reuse and weak patterns
- They’re static – attackers can steal them once and reuse them indefinitely
Passwords provide no contextual awareness and no assurance that the user is actually who they claim to be.
A Mobile-First World Needs Passwordless Security
Statista predicts that [object Object] will be using smartphones for digital interactions by 2021. Relying on 60-year-old password technology in this mobile-first environment simply doesn’t make sense.
Users want fast, secure, and frictionless access—without compromising privacy. Businesses want to reduce breaches and eliminate support overhead from password resets and lockouts.
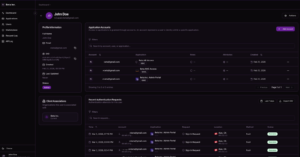
The Path Forward: Decentralized, Passwordless Authentication
The future of authentication is:
- 🔒 Decentralized – credentials live securely on a user’s device, not in a central database
- 📲 Biometric – users prove identity with fingerprint, face ID, or device possession
- ⛔ Phishing-resistant – no secrets to steal means attackers are blocked from the start
- ⚙️ Scalable – compatible with standards like SAML, OIDC, and REST APIs
Solutions like [object Object] platform enable this model—delivering friction-free access that’s secure by design.
Final Thought
Passwords have had a long run, but their time is up. We need to leave behind outdated systems that expose our data and adopt modern, password-free methods that match today’s threat landscape.
The shift has already begun. Will your organization lead—or fall behind?
FAQ: Why Passwords Are No Longer Enough
When were passwords invented?
In 1960, by Fernando Corbató at MIT, for protecting user accounts on a shared mainframe.
Why are passwords insecure?
They can be stolen, guessed, reused, or phished. Attackers use automation and social engineering to exploit them at scale.
What’s the alternative to passwords?
Passwordless authentication using biometrics, device-bound credentials, and cryptographic signatures.
How is this more secure?
There are no secrets to steal. Login approval happens on the user’s device, in real-time, with full context.