What is phishing and how can it be prevented?
Phishing is a type of cyberattack where threat actors impersonate trusted sources to trick users into sharing sensitive information like login credentials or financial data. Prevention requires eliminating credentials as a vulnerability, educating users, and deploying phishing-resistant authentication methods.
TL;DR
Phishing remains one of the top cybersecurity threats. It’s behind most breaches and is growing in sophistication thanks to AI. Protecting against it means eliminating passwords, implementing phishing-resistant multi-factor authentication, and giving users real-time context during access decisions.
The Rise of Phishing Attacks
Phishing continues to dominate cyberattack methods because it works—and it’s cheap. In 2023, phishing was responsible for:
- 36% of all breaches, according to the Verizon 2023 DBIR
- $2.7 billion in reported losses in the U.S. alone, per the FBI IC3 Report
- An 85% increase in phishing-related credential theft since 2020
AI-generated phishing emails, deepfake voicemail scams, and impersonation campaigns are becoming more convincing, faster to launch, and harder to detect.
Why Phishing Works
Phishing is a form of social engineering that exploits human trust. Attackers use fake emails, SMS, or websites to impersonate banks, SaaS tools, or employers—tricking people into:
- Clicking malicious links
- Entering credentials into fake login pages
- Downloading malware or ransomware
- Approving fraudulent access attempts
Once credentials are stolen, they’re often reused across services or sold on the dark web.
Shocking Stats on Phishing
- 91% of successful breaches begin with a phishing email
- 29% of all data breaches involve stolen credentials
- 2 million+ phishing sites were flagged by Google in a single year
- 81% of mobile phishing attacks originate outside of email
- 200% increase in compromised records during peak phishing surges
(Source: Verizon DBIR 2023, Google Safe Browsing Transparency Report, IC3)
Why Passwords Make Phishing So Effective
Passwords are the weakest link. Once stolen, they can be reused across accounts—especially when users rely on the same password patterns or use weak combinations. Even multi-factor authentication (MFA) isn’t immune, especially if it relies on SMS or app-based codes that can be intercepted or tricked through MFA fatigue attacks.
How to Prevent Phishing Attacks Effectively
1. Eliminate the Credential Threat Surface
Move away from passwords and implement [object Object]. That means:
- Passwordless access
- Tokenless MFA
- Device-bound biometrics
2. Implement Zero Trust Principles
Ensure that every access request is verified, authenticated, and authorized based on real-time context—not just a successful login.
3. Provide Real-Time Context to Users
Instead of approving a push notification blindly, users should be shown:
- What app is being accessed
- What transaction is being performed
- Where the request is coming from
This empowers them to stop malicious activity mid-attempt.
4. Choose a Platform Designed to Block Phishing
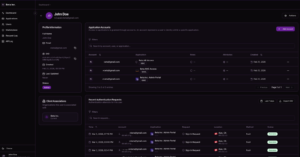
BlokSec’s [object Object] platform is designed from the ground up to prevent credential theft. Our decentralized, tri-factor authentication flow:
- Uses biometrics and digital signatures
- Provides full context for user approvals
- Requires no shared secrets or passwords
It’s simple, secure, and resistant to phishing—even AI-enhanced attacks.
Final Thought: Prevention Starts with the Right Strategy
Phishing isn’t going away. It’s evolving—fast. Defending against it requires moving from reactive security to [object Object]. That means investing in technologies that:
- Eliminate the root cause (credentials)
- Empower users with context
- Adapt to new attack techniques
The organizations that succeed will be the ones that harden their authentication surface while making the user experience simpler—not more complicated.
FAQ: Phishing Attacks & Prevention
What is phishing?
Phishing is a social engineering tactic where attackers impersonate trusted entities to trick users into revealing sensitive information or credentials.
How are phishing attacks evolving?
AI and automation have enabled more convincing, personalized phishing campaigns at scale. Attackers use SMS, email, and even phone calls to deceive users.
What’s the most effective way to prevent phishing?
Eliminate passwords. Use phishing-resistant methods like passwordless login, device-bound biometrics, and context-aware authorization.
Isn’t multi-factor authentication enough?
Legacy MFA (like SMS or app-based codes) can be bypassed. True phishing-resistant MFA uses cryptographic verification and removes shared secrets.
How does BlokSec help prevent phishing?
BlokSec eliminates passwords entirely and uses decentralized, context-rich, biometric-based authentication that can’t be phished or intercepted.
With no password to steal, phishing attempts fail at the first step.