Phishing attacks remain one of the most effective tactics used by cybercriminals to steal credentials, access systems, and move laterally inside organizations. Most breaches today still begin with someone clicking a link they shouldn’t—and relying on passwords or weak multi-factor authentication (MFA) gives attackers an easy path in.
Phishing-resistant authentication offers a stronger alternative. It removes shared secrets like passwords from the equation entirely and replaces them with device-bound credentials that can’t be phished or reused. Here’s a closer look at how it works, what it includes, and why more organizations are making the switch.
What Makes Authentication “Phishing-Resistant”?
Phishing-resistant authentication methods are designed so that even if a user is tricked into trying to log in to a malicious site, the attempt won’t succeed. These methods bind authentication to the user’s device, session, and context—eliminating the ability for an attacker to intercept and reuse a login attempt.
Unlike traditional MFA (which still often depends on usernames, passwords, and OTPs), phishing-resistant approaches don’t rely on secrets that can be harvested. They use cryptographic keys, biometrics, and protocols like FIDO2/WebAuthn to create secure, unphishable authentication flows.
Core Techniques That Prevent Phishing
Passwordless Authentication
Users log in without entering a password. Instead, access is granted using a cryptographic credential stored on a secure device, such as a phone or hardware key. Without a password to steal, phishing attempts are dead on arrival.
Biometric Verification
Fingerprint or facial recognition adds a layer of assurance tied directly to the user. Because these traits are unique and not transferable, they offer high trust with low friction—and can’t be phished.
Digital Signatures and Cryptographic Keys
Digital signatures use private keys stored securely on the user’s device to prove identity. The private key never leaves the device, and authentication requires real-time interaction from the user. There’s no static credential to steal, and phishing links won’t work because the authentication request must originate from a legitimate source.
Why Organizations Are Making the Switch
Better User Experience
Users are tired of password resets and clunky MFA tools. Passwordless and phishing-resistant methods reduce friction and speed up access while actually improving security.
Stops Credential Theft at the Source
If there are no credentials to steal, there’s no data to phish. Attackers can’t replay a cryptographic key or trick someone into handing over biometric data.
Builds Trust
Customers and employees expect security to be built in—not bolted on. Deploying phishing-resistant authentication shows a commitment to protecting identity and privacy, which strengthens relationships and reduces risk.
What’s Changed Since 2024?
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) now recommends phishing-resistant MFA for all federal agencies and critical infrastructure providers. Major cloud platforms are rolling out support for passkeys and FIDO2, and regulatory pressures around identity security are rising globally.
With AI-generated phishing campaigns and business email compromise (BEC) attacks on the rise, the bar for authentication is being raised across industries.
Final Word
Phishing-resistant authentication is no longer an emerging idea—it’s a necessary upgrade. Legacy MFA isn’t holding up against today’s threats, and relying on passwords puts users and organizations at risk.
The strongest path forward is clear: passwordless, phishing-resistant, and cryptographically bound to the user and their device.
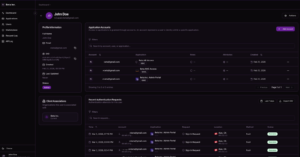
Learn How BlokSec Can Help
BlokSec’s [object Object] gives you a passwordless, phishing-resistant solution built to meet the security and usability demands of modern enterprises.
Talk to us about upgrading your authentication strategy—before attackers find a way in.