Passwords have a surprisingly short history for something so deeply embedded in digital identity. They were invented in 1961 at MIT, designed to solve a single narrow problem: letting researchers share time on an expensive mainframe without accessing each other’s files. They were never designed to secure the modern internet. Yet here we are, six decades later, still relying on the same basic concept to protect everything from bank accounts to healthcare records.
TL;DR
The history of passwords is a history of a broken system pressed into service far beyond its original design. Invented in 1961 at MIT to manage shared access to a university mainframe, passwords were never built for the scale or complexity of the modern internet. This article traces the history of passwords, follows the evolution of authentication systems, and sets the stage for the passwordless alternatives now replacing them.
Part 1: A Brief History of Passwords
Origin Story
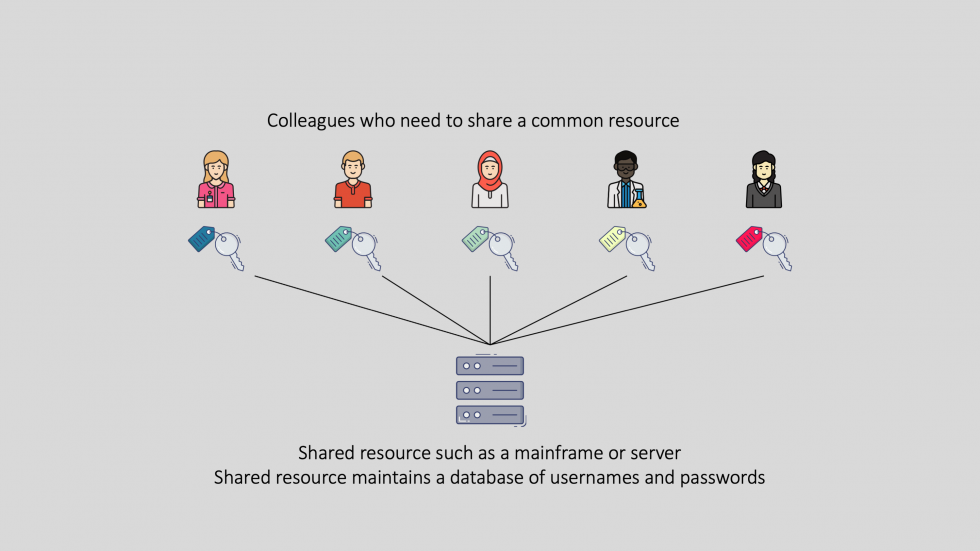
The first password system was built at MIT in 1961 to allow researchers to share computing time on the university’s mainframe while keeping their accounts private. Each user registered a secret word when their account was created. Repeating that word at login was supposed to prove it was the same person returning.
It did not take long for that assumption to break down. In 1962, a Ph.D. researcher figured out how to print the password file and use other researchers’ computing time without authorization. It is the first recorded incident of a computer breach, and it happened within a year of the password being invented.
The lesson was right there from the start: a shared secret is only as secure as the people and systems protecting it.
Legacy password systems
Passwords seemed like a good way to keep accounts private and secure, but it didn’t take long for someone clever to find a way around them. In 1962, Ph.D. researcher at the university figured out how to print the password file so he could use other researcher’s computer time. This is the first recorded incident of a computer breach.
Passwords and the Internet
For decades, password-based authentication remained a niche problem confined to academic and government computing. Then the internet changed everything.
As online services proliferated, every new account required two things: a way to identify the user, and a password to protect that identity. What had been a single shared computer in a university lab became millions of services, each holding a copy of your credentials. The attack surface for credential theft grew with every account created.
Today, the consequences are measurable. Stolen credentials are the leading cause of data breaches globally. Billions of username and password combinations have been exposed in public breach databases. The result is account takeover fraud, drained bank accounts, stolen identities, and billions in annual losses.
We are at an inflection point in the history of digital identity. The password has served as the default method of authentication for over sixty years. It has not kept pace with the threats built to defeat it.
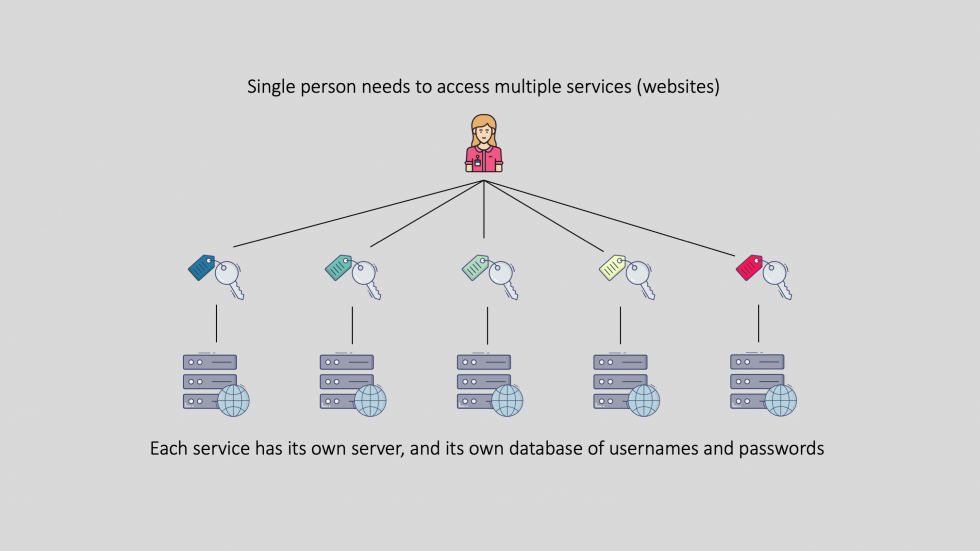
As online services exploded, so too did our use of passwords
As the number of online services steadily increased, there was a corresponding proliferation of identity information and passwords across the Internet. From an end-user perspective this caused a lot of frustration.
Today, the average North American has over 90 online accounts, with passwords for each. Remembering this many passwords is not realistic for humans, so to cope with the problem many people use the same password across many (or all) sites, or come up with a pattern that is easy to remember (but also easy to figure out). The problem, however, is this makes these users very vulnerable to hacking: it’s easy to download a script that will read a list of usernames and passwords and test logging in to millions of websites, looking for a successful match (this is called password stuffing).
All it takes is one bad website administrator or one data breach leaking credentials and the bad guys can gain access to all accounts that use the same password. The other alternative is to use a password manager such as [object Object] or [object Object] to generate random passwords and remember them for you under a single master password. But what happens if that master password gets compromised?
Single Sign-On (SSO)
In an attempt to resolve these shortcomings, a number of products emerged in the late 1990s and early 2000s called web access management or WAM for short. These solutions required an agent (this is a small application) to be installed on web servers, and these agents would intercept web traffic, log users in with a central server, then set a cookie in the user’s browser so subsequent requests would be marked as authenticated and allowed through. (This is an oversimplification, but I promised not to be too technical so I will leave it at that.) These new solutions were the beginning of web single sign-on or SSO, and if you have ever worked for a medium or large organization you’ve probably heard the term. Once an organization setup a WAM product, they could protect all their internal websites with agents, their users gained the convenience of signing in once with a single password.
This was all well and good if you were working at a company with an expensive, centralized web access management system, but it didn’t do much to help workers who wanted to access applications at another company or regular consumers trying to access online services. (In fact, dealing with customer identities was seen as so complex that it spawned a whole separate subdomain of IAM unimaginatively named customer identity and access management or CIAM). This leads us to our next evolution in passwords and online access.
Around 2002 a new standard appeared called Security Assertion Markup Language (SAML for short, since we technical folks love our three- and four-letter acronyms) with the goal of enabling organizations to share identity information through a trust relationship. The organizations involved could form a federation, allowing one organization to assert (vouch for) the authenticity of a user to the others. The new standard unlocked the ability for you to login once and access many services which could even be hosted by different companies. Because your home organization (called the identity provider) could assert your identity to the service providers, there was no need for the service providers to store a copy of your password. The identity provider could even share information about you behind the scenes, which at first seemed like a really good idea. (Spoiler alert: it wasn’t!) Incredibly, SAML (now in its second incarnation, SAML2, since 2005) is still commonly used today, but is relegated to intra-organizational single sign-on use cases where the issue of privacy is not a concern. This serves as an example of how slowly the world of information security adapts and evolves.
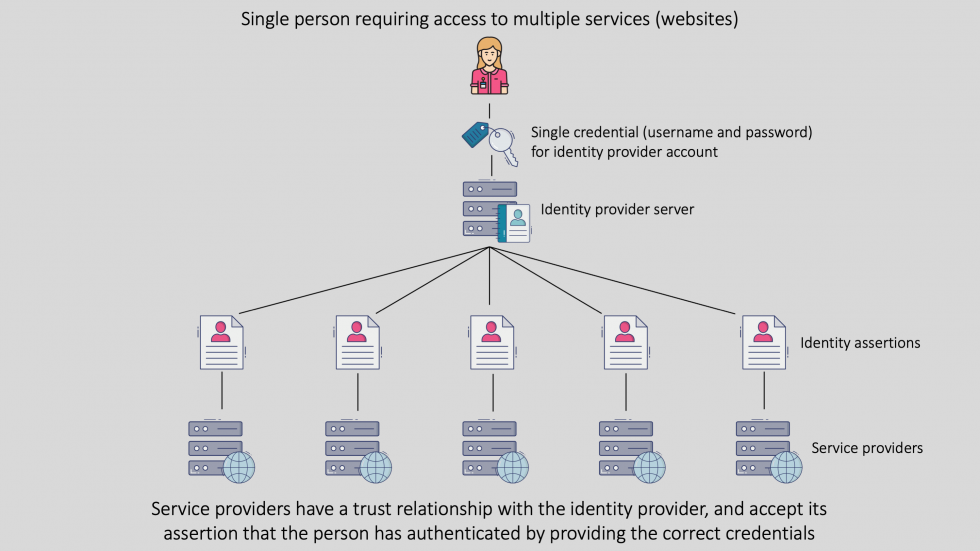
Single Sign-On (SSO) lets us log in once to access many services
As the standard started to become widely adopted, privacy advocates were quick to criticize that sending identity information in this way without the user’s authorization was trading privacy for convenience. To address these concerns as well as to add support for new types of applications such as mobile apps, additional standards were introduced over time. I will get into more detail in part 2 of the series, but eventually most services adopted the newest standard called OpenID Connect (OIDC). Like SAML, OIDC allows service providers to trust the identity of a user based on the authentication performed by an identity provider, but also specifies that users must grant their consent before identity details are shared. Most readers will have used OIDC perhaps without knowing it by name – if you’ve ever logged into a website using your Facebook, Twitter, LinkedIn, or Google account, you’ve used OIDC. Today, most consumer-facing websites and services offer the OpenID Connect method to users as a convenient way to sign up or login to their services.
What Comes Next?
The history of passwords is also the history of their failures. In the articles that follow, we will trace how authentication evolved from shared secrets to SMS codes to hardware tokens, why each step forward still left organizations exposed to credential-based attacks, and what phishing-resistant passwordless authentication looks like when deployed at enterprise scale.
This article is the first in a three-part series exploring the evolution of identity:
- Part 2 will cover current challenges and the gaps left by even modern authentication systems
- Part 3 will look ahead to innovations like decentralized identity and self-sovereign identity (SSI)—along with BlokSec’s vision for a passwordless future
FAQ: History and Future of Passwords
When were passwords first invented?
Passwords were first used in 1961 at MIT to manage access to shared mainframe computing resources.
Why are passwords a problem today?
They’re easily stolen, reused across sites, and difficult for users to manage—making them a top cause of security breaches.
What is Single Sign-On (SSO)?
SSO allows users to log in once and access multiple services without re-authenticating, typically within the same organization.
What is OpenID Connect?
OIDC is a standard that enables secure, consent-based identity federation for web and mobile apps. It powers many social login features.
What’s replacing passwords?
Modern solutions include passwordless authentication using biometrics and cryptographic keys, as well as emerging models like decentralized identity.