Why Mortgage Companies Are the #1 Target for Ransomware in 2025

Mortgage lenders hold the exact combination of assets that ransomware operators prize most: high-value transaction data, personally identifiable information (PII) on borrowers, and operational systems that cannot afford downtime during rate-sensitive periods. In 2024, the mortgage industry experienced it’s highest level of ransomware attacks, with 65% of financial services organizations stating they had been hit, […]
47 Million Mortgage Customers Breached in 18 Months: A Timeline of the Industry’s Credential Crisis
The mortgage industry has a credential problem. In the eighteen months between October 2023 and early 2025, more Americans had their mortgage data exposed than in the preceding decade combined. The companies involved were not fringe operators. They were some of the largest and most established names in the industry. And in case after case, […]
Password Reset Is Costing Your Mortgage Help Desk $50 Per Ticket — Here’s the Math

Your help desk manager probably knows the number. A senior IT professional once described their password reset load this way: a quarter of our tickets, every single day, for a problem that should not exist. The frustrating part is not the volume. It is that every one of those tickets represents a security vulnerability in […]
From Phishing to Foreclosure

How One Stolen Credential Can Take Down a Mortgage Operation It starts with an email. Nothing dramatic. No skull-and-crossbones icon, no urgent subject line demanding immediate action in red capital letters. Just a routine-looking message from what appears to be your secondary market investor portal, asking the loan officer to re-authenticate before accessing rate lock […]
When the Cloud Becomes Cover, MFA Fails: Why Identity Is the New Battleground

For years, security teams worried about the cloud being breached. Today, a more uncomfortable reality is emerging:the cloud is being used as cover. Recent threat analysis shows attackers increasingly operating from legitimate cloud platforms rather than attacking them directly. They rent infrastructure. They abuse SaaS tools. They leverage APIs and automation that look indistinguishable from […]
The Future of IAM is…

Recap: The Future of IAM – NKST Panel Discussion Missed our panel at the NKST IAM Summit? Don’t worry, we have summarized the high-stakes conversation for you. The overarching theme was clear: The perimeter hasn’t just moved; it has dissolved into a complex web of authority, AI, and human psychology. Here is a quick recap […]
Mr. Cooper Data Breach: What Happened, What It Cost, and Why “Secure Login” Still Wasn’t Secure Enough

In late October 2023, Mr. Cooper Group, one of the largest U.S. mortgage servicers, detected unauthorized access to parts of its environment and pulled key systems offline as a containment move. The disruption was not just an IT headache. It interrupted borrower-facing servicing workflows, rippled into mortgage market plumbing, and eventually escalated into one of […]
Phishing Attacks: The Path To Prevention

What is phishing and how can it be prevented? Phishing is a type of cyberattack where threat actors impersonate trusted sources to trick users into sharing sensitive information like login credentials or financial data. Prevention requires eliminating credentials as a vulnerability, educating users, and deploying phishing-resistant authentication methods. TL;DR Phishing remains one of the top […]
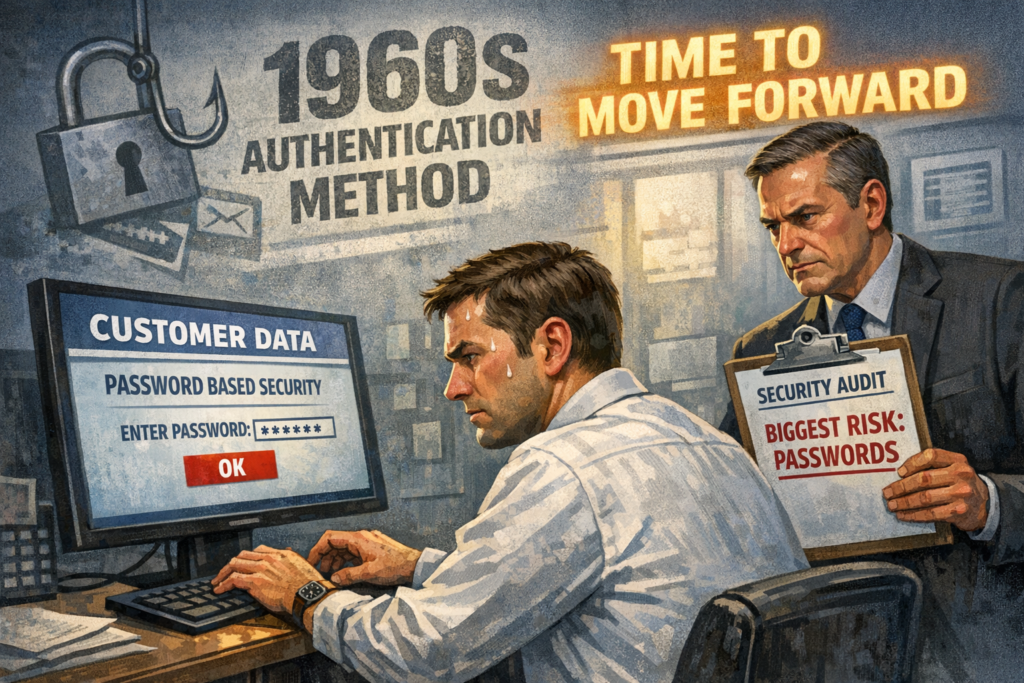
The Democratization of Identity – Part 1 – A Brief History of Passwords

Passwords were never meant to secure the modern internet. Learn how they started, why they’ve failed, and what’s coming next in digital identity.
3 ways passwordless authentication improves security and delights users

Passwordless authentication stops breaches and removes login frustration. Learn how it boosts security, eliminates resets, and delights your users.
